PROTECTION & SECURITY
TESTING
A key part of ibCom's approach to protecting your data is "test, test, test!" and to achieve this we base our testing strategy on the Open Web Application Security Project (OWASP) testing guide.
We apply particular focus to the OWASP Top 10 vulnerabilities.
Another key part of the ibCom's approach to protecting your data is "separation of concerns" and as per the diagram to the right - this gives us a testing advantage, as only have to test the infrequently changing "kernel" ie the mydigitalstructure.cloud interface (API).
All service endpoints are accessed via AWS Elastic Load-balancers.
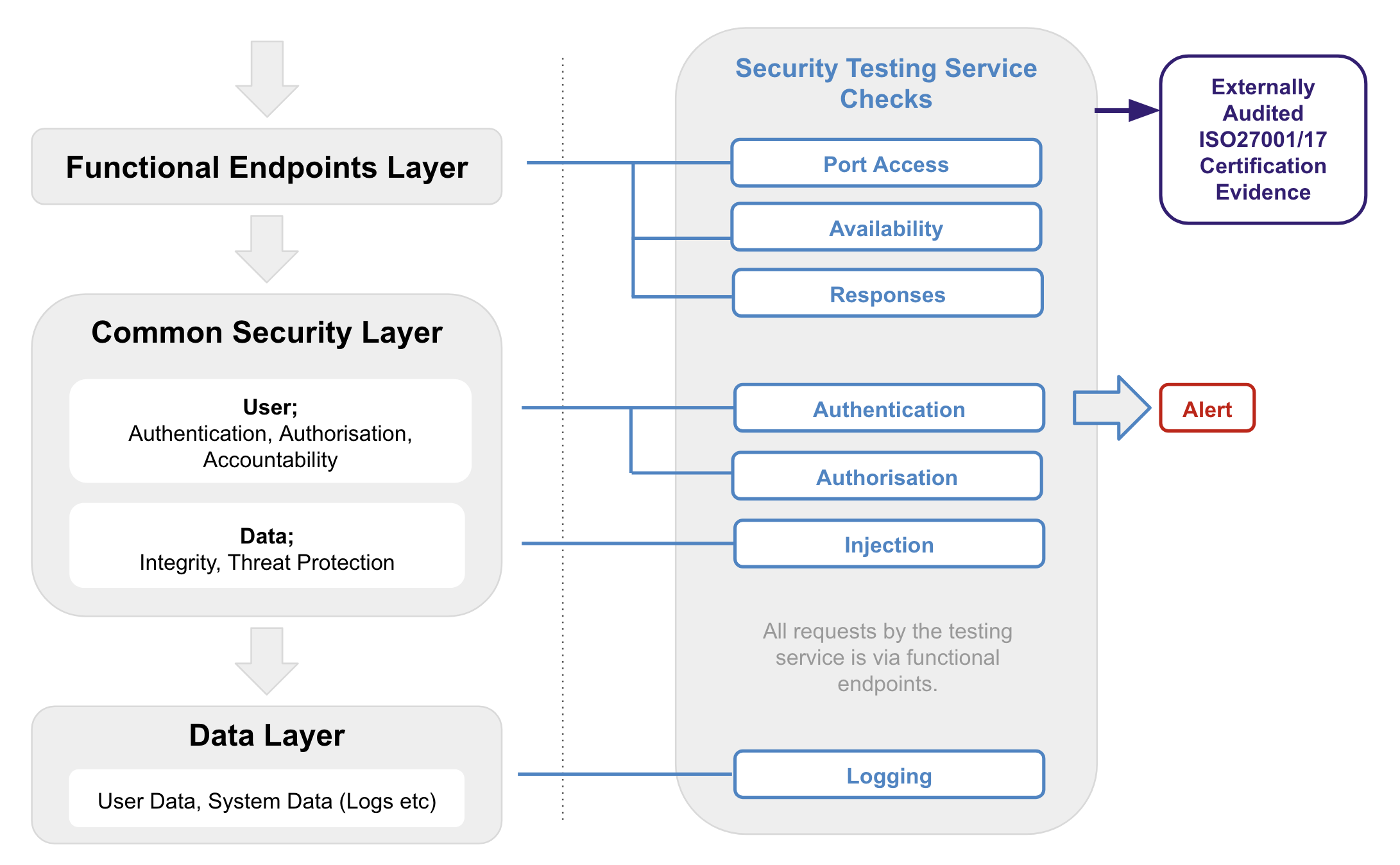
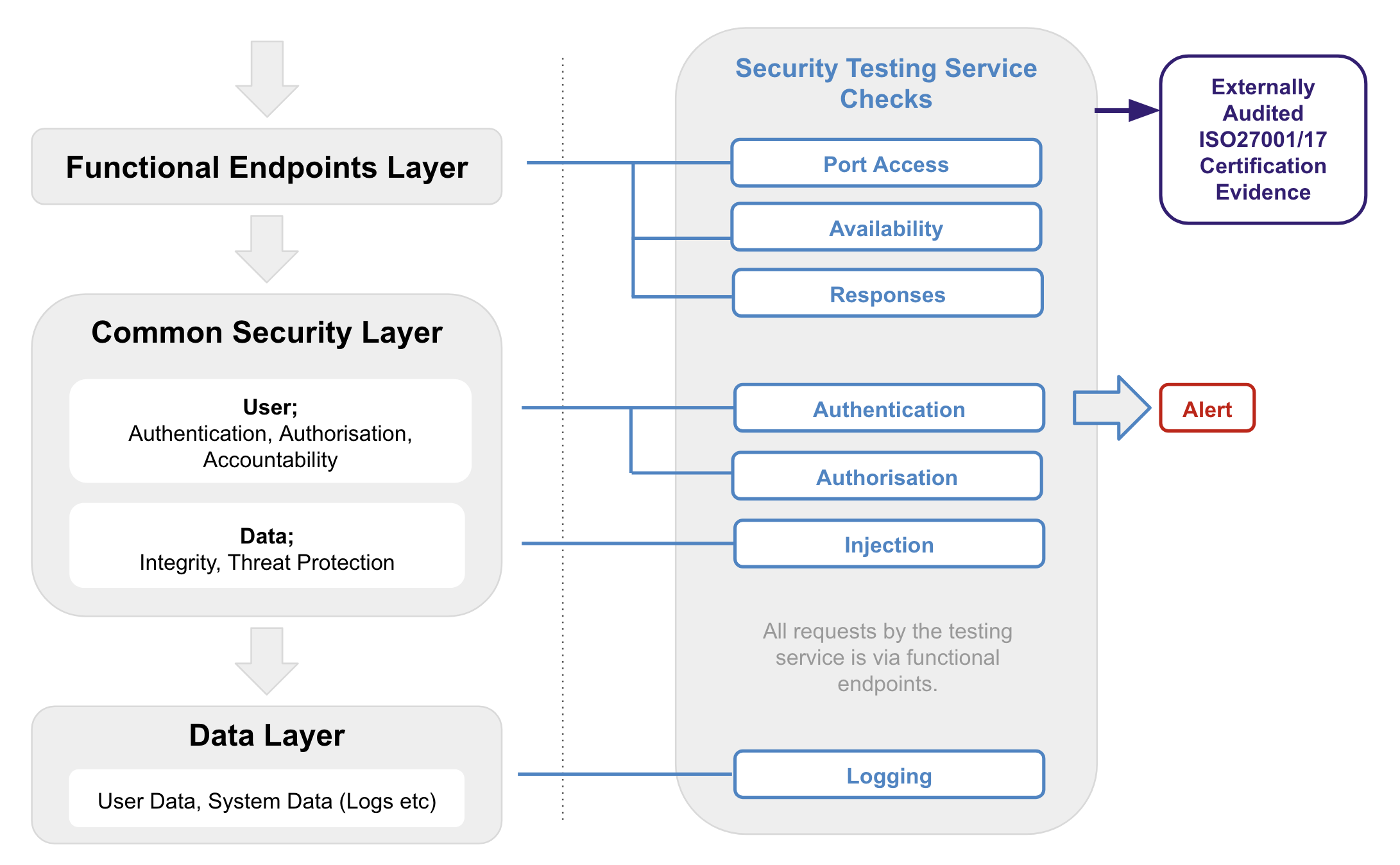
In addition to the OWSAP/nmap testing tools we use our own dedicated testing service to continuously test security via the functional service endpoints.
The testing service is run on an infrastructure service independent of the mydigitalstructure service.
This service tests for;
- Port access via scanning - ensuring only 80/443 if not authenticated and 443 if authenticated method.
- Authentication - including perfect forward security.
- Authorisation
- Availability
- Accountability; Monitoring & logging - checking that logging is occurring.
- http responses
- Injection - search & manage
Any exceptions to expected results trigger real-time alerts to ibCom operations.
Evidence of this testing is a key part of our external auditing of our Information Security Management System and compliance to ISO 27001/17.
SAMPLE OF REAL-TIME TESTING SERVICE TESTS...
| Test |
Testing service; |
Alert sent to ibCom operations if; |
| Logging |
- authenticates as known user.
- queries logs to check for logged authentication.
|
If no matching log. |
| Port access - scanning (Unauthenticated) |
|
If any port open that is not 80 or 443 |
| Port access (Authenticated method) |
- attempts to authenticate using port 80/http.
|
If response status not "ER". |
| Injection |
- queries the API with parameters with known sql injection techniques
|
If response status not "ER". |
| http Responses |
- queries the API and checks that no Server details returned
- Strict-Transport-Security header present
|
If Server name present. |
| Availability |
- check that service is available
|
If no response. |
| DNS checking |
|
If not found |
| SSL Checking |
|
If within one week |
INFRASTRUCTURE
Infrastructure is being constantly updated to deal with current threats and the Web Access Firewall uses the latest Control Sets to stay current.
We subscribe to daily update email services like Cyber Daily.
|